Articles
Publications
Preprint
- .
Improving success probability and embedding efficiency in code based steganography.
Preprint,
February,
2013.



Journals
- .
Block-PAD: A blockchain-enabled framework for resilient and flexible CBDC transactions leveraging digital identity.
Computer Networks,
pp. 111805,
April,
2026.


- .
Strengthening Biometric Fuzzy Vault Against Statistical Bias Exploitation.
Security and Cryptography,
pp. 139 -- 165,
November,
2025.



- .
Applied graph theory to security: A qualitative placement of security solutions within IoT networks.
Journal of Information Security and Applications. Vol. 55,
pp. 102640,
December,
2020.


- .
On the computation of the Möbius transform.
Theoretical Computer Science. Vol. 809,
pp. 171 - 188,
February,
2020.


- .
GREYCHashing: Combining Biometrics and Secret for Enhancing the Security of Protected Templates.
Future Generation Computer Systems. Vol. 101,
pp. 819 - 830,
December,
2019.


- .
On Generalized Reed-Solomon Codes Over Commutative and Noncommutative Rings.
IEEE Transactions on Information Theory. Vol. 59, number 9,
pp. 5882 - 5897,
September,
2013.



- .
On Quasi-Cyclic Codes as a Generalization of Cyclic Codes.
Finite Fields and Their
Applications. Vol. 18, issue 5,
pp. 904 - 919,
September,
2012.



- .
Wet paper codes and the dual distance in steganography.
Advances in Mathematics of
Communications. Vol. 6, number 3,
pp. 237 - 285,
August,
2012.


International conferences
- .
Systematization of Knowledge on Offline-Capable Digital-Currency Protocols.
ICFCDS,
april,
2026.


- .
A New Code-Based Formulation of the Fuzzy Vault Scheme.
ISC,
pp. 21,
October,
2025.



- .
Securing Offline CBDC Transactions: DigiVault Card and MarkoPayChain with Mobile Phone Integration.
ICIN,
pp. 33--40,
march,
2025.



- .
Fuzzy Vault Security Enhancement avoid Statistical Biases.
Secrypt,
pp. 12,
July,
2024.


- .
Securing Privacy in Offline Payment for Retail Central Bank Digital Currency: A Comprehensive Framework.
B2C,
october,
2023.


- .
A Side-Channel Attack against Classic McEliece when loading the Goppa Polynomial.
Africacrypt,
July,
2023.


- .
Cryptanalysis of a code-based identification scheme presented in CANS 2018.
I4CS,
pp. 3 - 19,
November,
2022.



- .
Reducing the Goppa polynomial search complexity using a Template Attack on Classic McEliece.
Poster at Africacrypt,
July,
2022.


- .
A semantic approach for comparing Fog ServicePlacement Problems.
IEEE International Symposium on Integrated Network Management,
pp. 4,
May,
2021.


- .
Placement optimization of IoT security solutions for edge computing based on graph theory.
International Performance Computing and Communications Conference,
October,
2019.



- .
Enhancing the Security of Transformation Based Biometric Template Protection Schemes.
CYBERWORLDS,
pp. 316 - 323,
October,
2018.



- .
Signature Renewal for Low Entropy Data.
IEEE TrustCom 18,
pp. 873 - 884,
July,
2018.



- .
Retrieving Dates in Smart Card Dumps is as Hard as Finding a Needle in a Haystack.
IEEE WIFS,
December,
2017.



- .
Memory carving can finally unveil your embedded personal data.
ARES,
pp. 9,
August,
2017.



- .
Memory Carving in Embedded Devices: Separate the Wheat from the Chaff.
Applied Cryptography and Network Security, ACNS 16,
pp. 592 - 608,
June,
2016.



- .
Image Watermarking With Biometric Data For Copyright Protection .
ARES - MFSec,
pp. 618 - 625,
August,
2015.




- .
Re-encoding reformulation and application to Welch-Berlekamp algorithm.
IEEE, ISIT'14,
pp. 1782 - 1786,
July,
2014.




- .
On the decoding of quasi-BCH codes.
International Workshop on Coding and Cryptography, WCC 2013,
April,
2013.



- .
Ensuring message embedding in wet paper steganography.
Institute of Mathematics and
its Applications International Conference -
IMACC11, LNCS Vol. 7089,
pp. 244 - 258,
December,
2011.



- .
List-decoding of binary Goppa codes
up to the binary Johnson bound.
IEEE, ITW'11,
pp. 229 - 233,
October,
2011.




- .
Key Reduction of McEliece's
Cryptosystem Using List Decoding.
IEEE, ISIT'11,
pp. 2681 - 2685,
August,
2011.



- .
New Set of Codes for the Maximum-Likelihood Decoding Problem.
YACC'10,
October,
2010.



National conferences
- .
IoT : Vers un contrôle des fonctionnalités au vu des menaces liées.
RESSI,
May,
2018.


- .
Tatouage d'images avec des données
biométriques révocables pour la preuve de propriété.
SAR-SSI 14,
May,
2014.


- .
Attaques algébriques.
MajecSTIC'08,
November,
2008.


Miscellaneous
Software
stegocurve
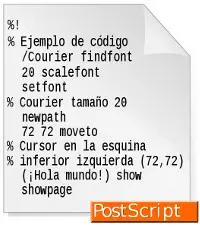
Description
The primary goal of stegocurve is to provide a simple tool for plotting curve from code based steganography. This is a standalone ANSI-C tool. It can be used for Unix and Windows computers. Any feedback is appreciated. stegocurve is under the GPLv3 licence.
All remarks or suggestions are useful, let me know by e-mail.
Download
You can download all the releases:
- stegogurve v1.2:
- stegogurve v1.1:
- stegocurve v1.0:
Documentation
You can find the full documentation generated by Doxygen in the archive, or for the lastest release in online documentation.
Students
- Formers
- Post-doc positions:
- 2018: 8 months Loubna Ghammam (currently Researcher at BOSH)
- 2017-2018: 1 year Kévin Atighehchi (associate professor at LIMOS)
- PhD:
- 2023-2026: Olivier Atangana (currently Research engineer at FIME)
- 2021-2025: Sara Majbour
- 2020-2023: Boly Seck (currently Research engineer at Alstom)
- 2017-2020: Tanguy Godquin (currently Director R&D at MailSPEC)
- 2014-2017: Thomas Gougeon (currently Research engineer at Thalès)
- Master degree:
- 2021: Sara Majbour (PhD)
- 2020: Sarah Grib
- 2018: Soufien Jabeur
- 2014: Thomas Gougeon
- 2011: Tania Richmond (Associate Professor -- ISEA)
- Post-doc positions:
Teaching
Since the 1st, September 2019, I am in charge of the Majeure "E-paiement & cybersecurity".
I contribute to different courses:
Miscellaneaous
- PhD defence participation:
- 26-03-23: co-advisor of the Olivier Atangana's thesis (Caen - France);
- 25-07-18: co-advisor of the Sara Majbour's thesis (Caen - France);
- 20-11-20: co-advisor of the Tanguy Godquin's thesis (Caen - France);
- 17-11-04: reviewer of the Birahime Diouf's thesis (Dakar - Senegal);
- 17-10-04: co-advisor of the Thomas Gougeon's thesis (Caen - France);
- 15-05-08: reviewer of the Idy Diop's thesis (Dakar - Senegal);
- 12-05-11: reviewer for the european mention of the Lorena Ronquillo's thesis (Barcelona - Spain);
- Jointly in charge of the Cryptology seminary of University of Caen.
- Organization committee:
- AfricaCrypt 2026;
- JSecIn 2018;
- ArCoCrypt 2018 - Arithmétique Code et Cryptographie;
- CAEN 2018 - Cryptography and Algorithmic Number Theory ;
- CORESA 2017;
- APVP 2014;
- JC2S 2011, 2012 and 2013.
-
Programme committee:
- Cyberworlds 2023;
- CYBER 2017 -- 2023;
- ArCoCrypt 2018 - Arithmétique Code et Cryptographie;
- IH&MMSEC 2013, 2014 and 2015;
- APVP 2014;
- JC2S 2011, 2012 and 2013.
- GREYC scientific leader for the Projet Investissement d'Avenir (PIA - french project) ID-Blockchain, from 2016 to 2018. This is an identity management project on a blockchain; respectful of user's privacy and trust of web.
Contact
| morgan.barbier{AT}unicaen.fr | |
|
ENSICAEN - GREYC 6, Boulevard Maréchal Juin 14 000 Caen CEDEX France |
|
| +33 (0)2 31 45 81 79 | |
| FB - room 330 |